


"A Special welcome to our visitors. And Feel free to get comfortable and make your self at home. Thank you for joining us. We have variety pages, information, news and resources! With lots to see and do. Enjoy your stay and may your day have smooth sailing! And thank you for your continued use and support of this website. "
TRANSLATE
Computer security information and virus information to help promote security awareness
According to leaders in the Anti-Virus industry, viruses are becoming less of a threat. But you should still be aware and keep your computers clean and up to date. It is important to make good use of your computers defragment and optimazation tools.
Computer Security Product Recommendations
Virus Information & Products
Computer Security
Security utilities allows you to restrict access to Windows important resources. Protect your privacy. K now who has used your computer. The administrator password prevents anybody to run the programs and change settings , install and uninstall programs.
Hacked: Who Else Is Using Your Computer? By Darren Miller
A friend called me one day and asked if I would stop by to look at his computer. He said it was running abnormally slow and he had found something on his hard-drive he could not explain. I could almost guess what it was he found. Have I been hacked?
You see, his computer had been hacked. Actually, in his case, his computer had been tagged.
Tag, You are It!
The file transfer protocol, commonly referred to as FTP, has been around for many years. In the early days of the Internet, it was one of the few ways to easily upload and download files from one computer to another. Many commercial operating systems come with an FTP server installed. In other cases, the option for FTP services is selected by a user when they are installing or updating their operating system. If this service is not setup properly, or you don not have an adequately configured software or hardware firewall, it is an open invitation for a hacker or intruder.
FTP Tagging - The most common purpose for someone to compromise your FTP server is for the storage and distribution of illegally obtained software and files. This could include cracked software, stolen movies, audio files, and pornography. Removing this type of contraband from your computer can be difficult, particularly if you are using a Microsoft Windows platform. Hackers use sophisticated scripts to create a maze of directory structures to house their wares on your computer. They may use a combination of names with spaces in them, and in some cases use extended characters (characters outside the normal alpha-numeric range). Deleting these directories through normal means may be difficult, if not impossible, for the average user. Many people wind up wiping their system and re-installing it, and that is if they are lucky enough to find out their system has been compromised.
The above is a perfect example of why the statement, I am not worried about being hacked. What do I have that a hacker would want? is not a good position to take. The fact is, you do have something they want, your computers resources. Why should a hacker store tons of illegally obtained files on their systems when they can use yours.
The Good, The Bad, And The Ugly
The Good
When I was young I use to spend hours upon hours on the Internet Relay Chat, also know as the IRC. The IRC is another method of Internet communication, which has been around for quite a long time. When I was a frequent user of the IRC, it was just plain fun. You would meet all kinds of people from all over the world. It was the instant messenger of the time.
The Bad
Today, the IRC is a huge communications network. It is made up of thousands of channels, and can be accessed by pretty much any operating system platform. It is also a favorite means of communication for hackers. They can discuss new exploits, methods of compromise, and even send and receive files. Many hacker groups use a cryptic language to communicate with each other on the IRC channels. Unless you know the language constructs they use, their conversations can look like a bunch of nonsense.
There are many exploits, backdoors, and Trojans that effect, or are contained in, the myriad of IRC clients on the Internet. Making sure you choose one that is relatively safe to use is not an easy task. As an example, take a look at this list of IRC safety and security info at IRCHelp.org.
The Ugly
It is not just the exploits and security risks associated with using the IRC, which need to concern you. If a hacker is able to install an IRC relay agent on your computer, it can become a conduit through which they communicate and distribute information. In my line of work, I have identified many systems with IRC backdoors or relay agents installed. The only thing the end user typically experiences is a decrease in system; performance and Internet access.
Just Open The Door And Let Them In - Peer-to-Peer File Sharing
If a total stranger were to knock on your door, and ask to come in to just hang out for awhile, would you let them in? Most likely not. If you are using peer-to-peer file sharing software to locate and download files on the Internet, you are opening the door to destruction. Many of the file sharing services and software available on the Internet today tout themselves as being safe and clean. This is as far from the truth as you can get. If you are a regular user of these services, the chance of your computer being back-doored or hacked is significant.
If you have anti-virus software installed (and up-to-date), you are undoubtedly received messages regarding viruses when downloading files from peer-to-peer services. These are not the only things you could be downloading. Many hackers imbed root-kits in files and distribute them using peer-to-peer file sharing. Root kits contain many types of tools used by hackers to gain control over computers. If the installation of the kit on your computer goes undetected and is successful, it is only a matter of time before your computer is completely compromised.
I can not tell you how many times I have found company employees (and technical personnel) using peer-to-peer file sharing services. Any organization that permits this is putting itself at risk. And, the risk is much greater as compared to a single home computer because of the number of potential internal targets.
Conclusion
Of course, the above is just a few examples of different methods and types of computer compromise. There are many ways your computer can be hacked. Your best defense is a good offense along with education and awareness. When you configure your computer make sure you enable only the software and services that you need. Many programs have known exploits and / or require additional steps be taken to adequately secure them.
Do not make the assumption that you are not a target just because you do not think you have anything of interest on your computer.
If your computer becomes unstable or dramatically decreases in performance, do not assume it us just a quirk or that it is time to upgrade.
Make sure you have a software or hardware firewall in place to protect you from the Internet. Your firewall should be configured not to allow anonymous inbound access from the Internet. This is the default configuration for most firewalls, but you should make sure the one you are using is properly configured.
Make sure you have adequate virus and spyware protection, and your pattern signatures are up-to-date. Many anti-virus applications work on a subscription basis. It is not uncommon to find out your subscription expired. If it is expired, your software may not protect you from new and emerging threats.
And, do what ever you can to stay away from any type of Internet peer-to-peer file sharing service. No matter how safe the developer claims it is.
About The Author
Darren Miller is an Information Security Consultant with over sixteen years experience. He has written many technology & security articles, some of which have been published in nationally circulated magazines & periodicals.
Special Tahnks to Darren. Helping you secure your home, home office, or small business computers and technology. Darren is Staff writer for several other e-zines.
Provides an always-on and automated, all-in-one PC care service with anti-spyware, privacy protection, performance tune-ups and system cleaning functions.
Advanced System Care 7 PRO (3PCs with EBook)
At a great price. Only $19.99.
Download and try first: Download Advanced System Care 7 PRO (3PCs with EBook)
More Software
Yes we have more! Checkout Software Electronically Downloadable Plus CDs Software
***** Sponsored *****
Disclosure: We may earn from our sponcers.


Your 125x125 banner will appear on Three related pages of a2000greetings.com Your Banner Ad Here!
Thanks To Our Sponsors
Ad earnings help this web site.
VPS Hosting with Full root access in a fully scalable hosting environment. Starts at $34.99/mounth. Learn more
Wine is good anytime. And makes for great Gifts of Wine
Manage users computer and mobile activities anytime, anywhere as they happen. Monitor Filter Control Demos available.
Software
Wine Express
HostGator Optimized for Speed and Security
Earnings Disclaimer
Ads: Earnings Disclaimer
Ads:
Flowers Ad: Lots of Fonts
 Ad: Earnings Disclaimer
Ad: Earnings Disclaimer
Thank You for your continued support.
Donations for A2000greetings
We ourselves feel that what we are doing is just a drop in the ocean. But the ocean would be less because of that missing drop. By ~ Mother Teresa

We have variety pages, information, news and resources! With lots to see and do. Enjoy your stay and may your day have smooth sailing!
SITE MAP
Home a2000greetings.com
National Anthem of the Republic of Ireland
Shopping easya2000greetings Community Forum
USA
United States Of America Information
The Declaration Of Independence
Signers Of The Declaration Of Independence
BALD EAGLE AMERICAS NATIONAL EMBLEM
Aerospace & Defence & Astronomy
Entertainment
Puzzle IQ Test Brain Test Young
Investors Confuse The Familiar With The Safe
Plus Alternative Medicine Information and News
![]()
Carousel Carousels The Golden Age
Poetry
Wolf Poem Miracles In the Snow
AnimalsANIMALS
Dog Smart Grooming And Boarding Needs
The Wolves Legend of Two Wolves
Holistic Approach to Pet Health Care
Animal Meaning Spirit Animal Totem
Poem Lend Me A Pup
Golden Retriever Irish Setter Magic
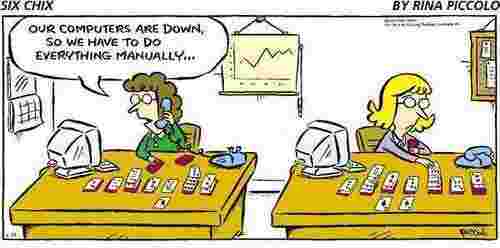
We do hope you enjoy this Humor section HUMOR / Comedy / JOKES
Humor
Five Houses of Worship with Squirrels
Police Man Did You Laugh Today
Top 10 Things only Women Understand
Funny Pocket Tazer Stun Gun Story
Some Deep thinking from George Carlin
Family Resources

Children's Safety Helping Kids at a2000greetings Helping children with a personal touch, children's safety. A200greetings has information for helping kids around the world. Protect kids for generations.
There Must Be No More Carlies, Article by: Linda Spagnoli
PEOPLE HELPING PEOPLE For Humanity
MothersMother's Day Word Scramble Search Puzzle
Covid-19 & RSV Virus Information
INDIAN
American Indian Information
Indian Search Puzzle Printable
Wolves In Native American Folklore
Books and author of best native American fiction in 2011.
Bridal and Wedding
Planning a Wedding and Organizing a Bridal Shower
Brides Maids Dress Up Game Play
Games
Toys Games
Family Resorces
Play Glitter GamePlay Shrek Forever After Puzzle
Play Tetris Tetricopy Explorer
Puzzles
Puzzle IQ Test
Crossword Puzzles Daily Online Play
Indian word search puzzle Printable
Puzzle Software Puzzle Applet Puzzle World Games
Check our holiday section for lots more puzzles.
Casino
Casino Game Fun
Software
Software Electronically Downloadable
Software To Edit Modern HTML5, PHP and CSS3-Based Websites
Web Site Management Software at a2000greetings
Software : Audio : Featured Tracks
Virus Information and Products
Business for Windows Based Software
Automation schedule recurring tasks Workshop Software
Convert animated GIFs to Adobe SWF file format
Free RX Discount Card Printer Friendly
Articles
Get to know Jerrie Cobb Who's Driving the Bus?
Holistic Approach to Pet Health Care
Dog smart policy for your dogs grooming and boarding needs Basics of Dog Training
Organize Your Stuf Five Minute Organizing
Organizing Your Home Or OfficeGifts for him or her for the Holiday's
What Men Really Don't
Want for Fathers Day
15 Minutes A Day To Organizing Your Home Office - Advanced tasks and schedules manager software
Website Usability Leads to Conversions
Increase Your Web Site
Traffic By Using
Keyword Articles
How to Build a Website Around Keywords
How to Increase the Ranking of Your
Page
The Perfect Book and Where to Find It
How To Create Multiple Streams of Online Income
One of my favorite things about being an Internet Entrepreneur is that I can literally wake up in the morning with an idea for a new product and have it become a reality by the afternoon. Or I can find new ways to promote an existing product. Or I can join a new affiliate program or pursue a joint venture. Every time I repeat this process I create a new stream of income to add to my existing revenue base.
Read more;
The Perfect Home Based Business
Are you looking for a Business you can Work at Home? Did you know that a Work at Home Business is the dream of millions of Americans, and millions more world wide? It is estimated that over 68% of us will have some kind of Home Business to help supplement our income. Plus, numerous surveys show that a Business of your own is still the #1 way for the average person to achieve financial freedom and independence. Read-More The Perfect Home Based Business
a2000 Greetings Flash Games
Helps tens thousands amateurs and professionals involved in stock photography in preparing and uploading their images to leading stock photo agencies.. a2000 Greetings Flash Games
How To Market Your Home Business On A Shoestring Budget
Ways To Generate Online Income
Self Publishing for profit and pleasure
Creating Your Professional Image on the Internet
Design Solutions-Take
your website to a new height
How To Set Up A Professional Website On Your Own Using Web Templates
Free Traffic Exchanges are King
How Traffic Exchange Sites Work
Making Targeted Traffic Work for You
Build websites easier with premade templates
Google Wants To Help You Succeed
Listed Websites Affect Rankings
We are allways adding more to Family Holidays
Family Holidays
Happy Easter
Easter Mom Ma And Easter Memories
Father's Day Contest Story - a2000greetings
Mother's Day Word Scramble Search Puzzle
4th Of July or July 4th Celebration
- Valentine's day
- Romantic Love by Paul Faulkner
- Traditional Valentine's Day
- Love Quotes
- Romantic Story
With a pinch of the luck of the Irish and hug.
 -
- 
Happy St. Patrick's Day Welcome Bishop of Ireland
The four-leaf clover is Ireland's Favorite Token of Good Fortune
An Irish Friendship Wish
The National Anthem of the Republic of Ireland & Irish National Anthem Gaelic
St. Patrick's Day Word Search Puzzle Free
St. Patrick's Day Child Maze Printable(Free)
Thanksgiving Word Search Printable {Free}
Santa's Comming To Town
- Santa Is Coming To Town
- Claus
- St. Nicholas
- Santa Claus's First Portrait
- A Christmas Wish
Welcome to a Merry Christmas and Happy Holiday!
Welcome to the Christmas Time - Animated Wallpaper
Halloween Fun Scare(Our Other Site)
Spirit Pages
Garden Of Friendship
a2000greetings website guardian angel came out looking like my mom.
Angels Of The Garden
Heart -N- Soul
Our WOSIB 2008 Anniversary Page One
Our WOSIB 2008 Anniversary Page Two Adoptions for Us
Webmail
![]()
a2000greetings Fun Free Professional and Customizable E -mail Cards
Coronavirus & RSV - a2000greetings
Ebooks
Action Figures2
Action Figures and Bobble Heads
Computer Security Virus Information & Tools
Greeting Card Software
Pheromones
Harry Potter Gifts
Poster Prints & Custom Framing
Community
Welcome to a2000greetings Community Forum - Index
Computer Geeks make Better Husbands
Top 12 Things Not To Say To A Cop
Golden Retriever Irish Setter Magic
Bald Eagle Americas National Emblem
Web Directories
Search Engine Web Directory
Website
Webmaster Resources
Webmaster Resources & WEBSITE BUILDING
Webmasters Tech resources easy webmaster solutions
Resources for Webmasters at a2000greetings
My IP unique ID Address IP Number
Keywords Information For Webmaster at a2000greetings
Search All Website Search Ideas Search Articles
Color Chart is popular with web developers
Leverage Browser Caching Positive Company Branding
Make 3D Headings and Banners Free
Web Site Building at a2000greetings
Easy Banner Web Site Ad Rotator
WEBSITE CONTENT
Free Website Content Page 1
Things for your site Page 2
More Free Content For Websites Page 3
Website Templates All Kinds Halloween Pumpkin Carving Templates More Business and Finance Website Templates Flash Templates
Twas The Byte Before Christmas
Revolution Studio & Dreamcard
Palmdevice
Guest Book
PRODUCTS
Software To Edit Modern HTML5, PHP and CSS3-Based Websites
Organizer Planner Software, & Ebooks
A2000greetings SAFE SITE
SSL Report: Cerficiate A a2000greetings.com
Positive SSL A2000greetings Trust Certificate
Norton-Secured

 Safe Surf Rating for a2000greetings. Certification Child Safe For Web Design and Developers
Safe Surf Rating for a2000greetings. Certification Child Safe For Web Design and Developers
Check page rank. a2000greetings Google PageRank: 4/10
a2000greetings on Directory en Geovisites Website Worth $361,659. PR Score 4.9
Designed: By Susan an a2000greetings brand. Our Brands Halloween Fun Scare International Haunted House | Add Babies | Webhost-Websites | Our Holiday Site | 2000greetings

 Positive SSL A2000greetings Trust Certificate
Positive SSL A2000greetings Trust Certificate SSL Report: Overall Rating A www.a2000greetings.com (198.38.82.143)
SSL Report: Overall Rating A www.a2000greetings.com (198.38.82.143)
a2000greetings Code OF Ethics - Advertise - Comments Policy - Contact Us - Disclaimer Earnings Income - Disclosure Policy - Privacy & Cookies Policy - Public Relations / Press Release - Spam Policy At A2000greetings - Terms Of Use - Trust
THANK YOU
"We have variety pages, information, news and resources! With lots to see and do. Thank you for joining us and for visiting our family friendly, multi functional web site portal. And for your continued use and suppoet of this website. Enjoy your stay and may your day have smooth sailing! And be uplifted from start to end and filled with sunshine and warmth, joy and happiness and be untroubled and serene in all that you do.
Please Support A2000greetings.com As a Verified Member of PayPal. We use E-commerce services pages for safe downloads and sales. Your payments are securely processed. We proudly display the PayPal Seal on our website. Sales, Ads and your Donations help to keep this website going.
Donate to A2000greetings. It's fast just click the fast PayPal Seal!"

"Thank You ~ a2000greetings.com"
Add your advertisement. Get a quote for your ad sent info (to) ad at a2000greetings.com.